Insider Threat for Remote Workforces
Today we are seeing a greater number of employees working remotely than ever before. This may be due to some reasons known to the company and the worker or because of some general reasons like proximity, space at the workplace or due to the current pandemic. Nowadays, most companies prefer to maintain a small workspace and have most of their employees work from their convenient places.
With the emergence of the COVID-19 pandemic this type of employment and workforce is the most preferred and in some case the only option some companies have. Due to the effect of the lockdown production and productivity of many companies has been put to the test and the only way to keep up with the organizations activity is to have people work from their homes. Many organizations still prefer to have their workers work from home. The reasons can vary from employer to employer. Some find that employee productivity is increased, some find they save money and space and some have the employee’s health and safety as the determining factor.
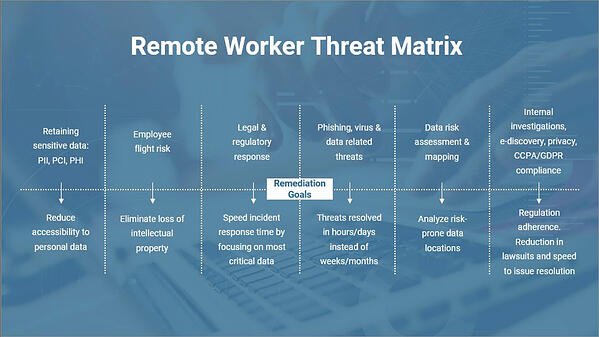
Nevertheless, the effectiveness of this type of employment may begin to dwindle because of an insider threats. Insider threats occurs when an employee with a certain degree of access causes any form of harm to the organization especially by data exfiltration. Insider threat amounts to privilege misuse and consequently the company may stand the chance of losing their competitive advantage or other harms like hacking and phishing.
This is a great security threat which may instigate an organization to reconsider their option for a remote workforce, but given that the situation at hand (the pandemic) has made it imperative for a remote workforce to ensure steady productivity, how can an organization manage or curb insider threats?
In answering this question, it is good to mention that there are two categories of insider threats. The first category is the unaware insider while the second category is the intentional or malicious insider.
- The unaware insider: this category of insider is the organization’s regular employee who has no intention of causing any harm but because of negligence and lack of carefulness exposes the company to harm. Here are a few examples:
- Misdirected Emails: At one point or the other we might have sent mail to the wrong recipient. Sometimes this seamless little error can cause an organization direly as some emails might contain sensitive data and is meant only for the specified recipient. It can be very difficult to recall such emails exposing the company's data.
- Phishing: Scammers often deploy phishing attacks and other social engineering tactics in order to breach both companies and individuals to gain access to confidential data or to try and use a network of a particular organization to carry out wire transfers. If a staff member were to be a victim of this, it might have adverse effects.
- Loss of work device: Sometimes individuals misplace their work device or it might be stolen from them. This might place the organization at risk as the thieves might uncover sensitive data leaving the company at their mercy.
- Third party agency: when a third-party agency much like a vendor or contractor has a very weak and less secured portal, information shared with them might be at risk as they can easily experience data breach.
- The intentional or the malicious insider: This set of insiders are out to cause harm to the organization mostly because they have an axe to grind with the organization, or for monetary gains. This might be a result of layoffs, demotion, salary reduction or personal issues with top management. These are some ways the malicious insiders operate:
- Competitive Edge: Aggrieved staff members might use an company's data in their possession to get a much better deal with a new firm. such that might include client list, operations tactics, new product patent and other trade secrets.
- Financial incentive: Data brokering is a very lucrative industry, estimated to be worth over $200 billion. Some individuals will take advantage of this offer and sell good and important information their company for their financial gain.
- Revenge: a staff member or former staff member may have a bone to pick with a company and will pose and a candidate for employment and once they get the job, they will execute their revenge plan by exfiltration of their data.
How to Manage Threats from a Remote Workforce
There are some activities and policies a company must adopt in order to manage and reduce the risk of insider threat for a remote workforce. Some of this policies and activities include:
- Have a risk assessment conducted for remote employees: this assessment is usually the first thing to do when considering employees to work remotely. Risk assessment will help a company determine the threats, the possibility of risk occurrence and how heavy it may affect the company if it should happen.
- Reduce remote access to highly sensitive data: making sure that the remote workforce do not have total access to highly sensitive data without clearance from the board members. This will help monitor the activities of the remote workforce and every suspicious activity could be monitored and tracked before it could cause heavy damage.
- Use a telecommuting policy: telecommuting policy will channel every form of communication to a central place which will help the company monitor every form of communication involving every employee. This policy also contains the remote working condition for the company. The working condition may include communication guidelines, the consequences of skipping the requirement for telecommuting, cybersecurity tools for a remote worker among others.
- Inform remote employees about cybersecurity and improve your security through feedback: most of the remote workers may not have good working knowledge of cybersecurity and its effect when hacked. It is the duty of the company upon hiring to educate the remote employee on cybersecurity and how to control its occurrence. Also, the company should have a system where they get feedback on their security from their employees and customers. This way, they will know how much they have improved, what they still have to do and the general idea of people on their security.
By Joseph Sordi, SVP
Strategic Security Corp.